Posts
-
Chunk an Iterator into Arrays in PHP
PHP's iterators can take the heat out of memory consumption when processing big datasets. Typical for such datasets is that workers process them in manageable chunks of a limited size. As these workers typically are independent of each other, it might be necessary to pack chunks of the source in arrays that can be sent with the job metadata to the worker. This is when you might want to chunk an iterator into arrays.
A Generator function is useful to achieve this purpose. As opposed to a normal function, a generator function yields return values as the caller asks for them. Take this dice roller:
function dice() { return rand() % 6 + 1; } -
Secure an NGINX Docker container with Let's Encrypt
For web-applications, securing the communication between client and application is essential. As containerisation of such applications becomes the standard, I will be looking into one another method to achieve SSL encryption with a containerised NGINX web server using Let’s Encrypt.
A full-blown multi-application server typically runs a web server that hosts applications. To secure the communication between this server and clients, a secure (HTTPS) connection is initiated that uses an SSL/TLS certificate and a corresponding key to encrypt the data on a per-domain basis. A trusted Certificate Authority like Let’s Encrypt can issue certificates that indicate that you are the valid owner of a domain. To proof this ownership, Let’s Encrypt uses a protocol called ACME. Tools like CertBot and acme.sh implements this protocol and can as such allow you to obtain and renew SSL/TLS certificates signed by the Let’s Encrypt CA.
Figure 1: Infrastructure of a server with 2 public IP addresses, one hosting two applications through a proxying webserver and another with a dedicated application webserver.
-
Compact `switch` alternative
Some situations in PHP require a set of variables to have values depending on some condition. To achieve such
variable -assignment, a switch statement is the traditional GOTO, but PHP’s array syntax combined with thelist()language construct. -
Filtering and Control Library
Check out this header-only C++11 library of control and filter tools. Currently it features PID control, bi-quads (or second-order-sections), state-space systems and a PRBS (pseudo-random-binary-signal) system identification function.
The code-documentation and tests provide reference and example to use the library. Creating a second order floating-point state-space is easy:
-
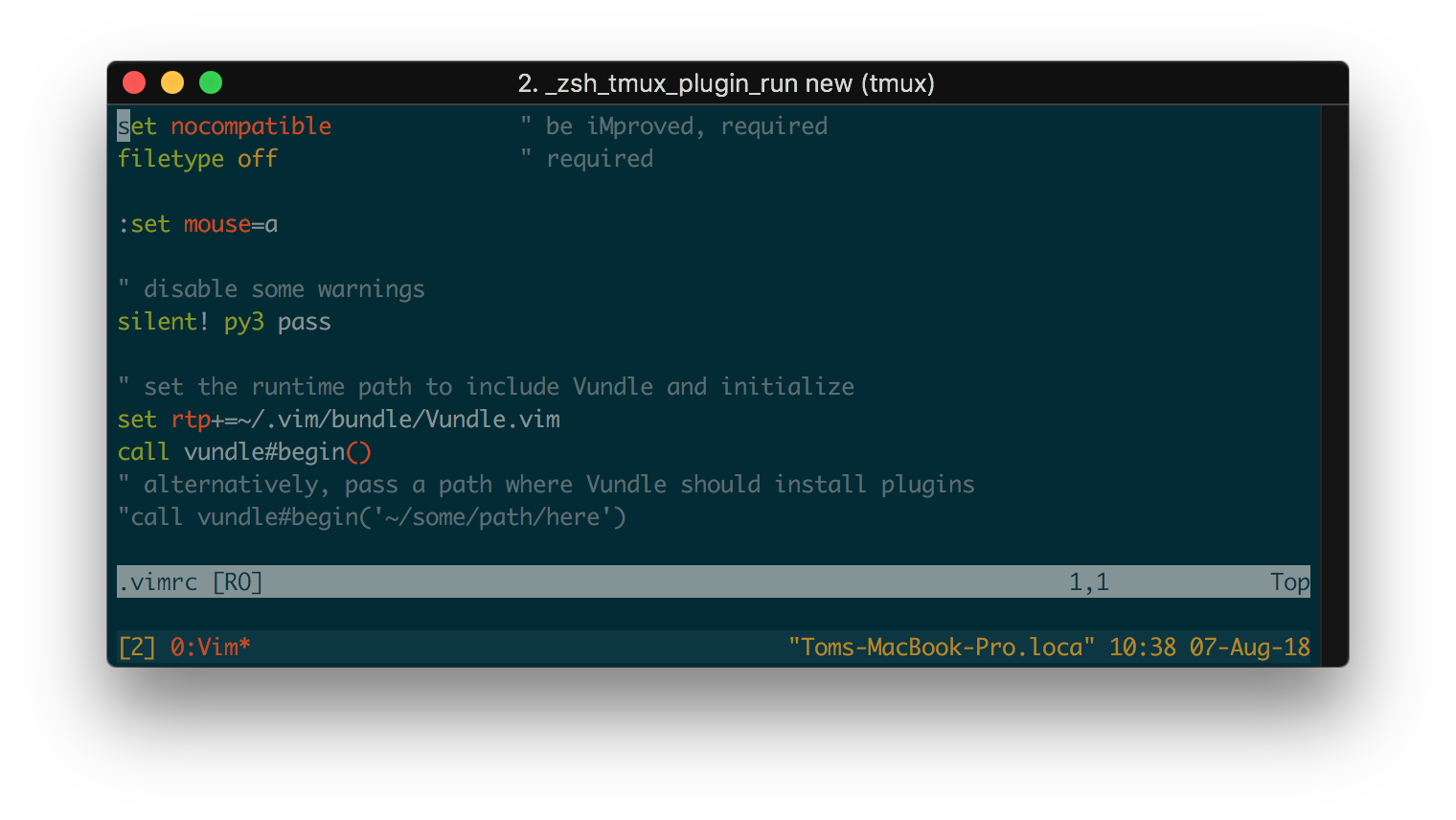
True color support with (iTerm2 + tmux + Vim)
The terminal can be an effective workhorse for achieving a job. It is fast and agile and allows you to do get things done that would have taken you much more time than when you are limited to using the graphical user interface alone. The GUI, however, treated us with elegant visuals and a clear design that made working with it a comfortable experience that is easy on the eye. When working a lot in the terminal, one might want to borrow a piece of this visual experience in the form of an attractive true color terminal.
There is, however, some configuring to do to get a true color scheme working on a terminal emulator like iTerm, especially when combined with a terminal multiplexer like tmux.
-
Quick-fix: MATLAB FMU import error
MATLAB 2017b introduced support for the Functional Mock-up Standard by providing FMU-import blocks in Simulink. This open standard enables mixing of simulation models created with different tools, like prototype controllers before coding them. This is an extremely powerful feature that I will write more about in soon. This memo, however, is about an error that occurred to me when importing an FMU in Simulink and how to fix it.
The error is something like:
Error parsing FMU <fmu-name>. Caused by: Error in supplied FMU: Dynamic library file <lib-file> does not exist in FMU <fmu-name>.

Error parsing FMU ‘dq.fmu’. Caused by: – Error in supplied FMU: Dynamic library file (‘dq.dylib’) does not exist in FMU ‘dq.fmu’. -
Fixing: Vagrant LXC error, mount.nfs: mount to NFS server 10.0.3.1:/path failed: timed out, giving up
Vagrant-LXC is a plugin that provides integration of Vagrant with LXC containers, a modern virtualisation technology native to Linux. To share files between the host and the container, NFS can be used. The Vagrant NFS plugin ensures that a NFS server runs at the host that exports predefined locations of the host’s filesystem. Sometimes, an error pops up when starting a Vagrant box, indicating that a timeout occurred and that starting the box failed.
A typical error is as follows:
mount.nfs: mount to NFS server ‘10.0.3.1:/path’ failed: timed out, giving up
Which means that the connection is blocked, often due to the firewall. Another error might be something like:
mount.nfs: access denied by server while mounting 10.0.3.1:/path
This practically means that the container is not allowed to reach the NFS server of the host, often due to AppArmor policy. I experienced this issue some time ago and discussed it in an issue at Github.
-
Symlinks cause ‘Not valid template file’ in Magento 1.9.3.4
Keeping Magento shops up to date is important to reduce their vulnerability. Sometimes, security updates introduce breaking changes. The recent Magento update, version 1.9.3.4, includes such a breaking change that can cause blank pages on the front-end and back-end. This is caused by the way in which Magento handles symlinks.
When blank pages occur, take a look at Magento’s system.log file. You might find entries like the following:
2017-07-20T20:53:05+00:00 CRIT (2): Not valid template file:frontend/theme/default/template/page/2columns-right.phtml 2017-07-20T20:55:48+00:00 CRIT (2): Not valid template file:adminhtml/default/default/template/mstcore/toolbar.phtml 2017-07-20T20:55:48+00:00 CRIT (2): Not valid template file:adminhtml/default/default/template/magmodules/beslist/notifications.phtml
-
Import Remote Database Directly over SSH
Developing, maintaining and debugging web-applications often involves copying a remote database to a local or another remote machine. This post lists a number of methods that I find useful. It acts as a reference for myself which I happily update and improve based on comments and experience. My favourite method: stream the database dump directly to the target machine.
I assume a MySQL or MariaDB database on a Unix or Mac OS machine but by adjusting the appropriate commands most of these methods apply to other databases as well.
-
Configuring MySQL with .my.cnf file
Connecting to a MySQL server often involves providing hostnames, usernames and passwords. Use a .my.cnf configuration file to provide defaults that simplify working with a MySQL server.
Providing a default password reduces security. Take effort to make sure that the password cannot be read by other users on the system. If the server runs locally, use credentials that are only allowed to connect locally.
subscribe via RSS
